Five ways to plan information security education│What is the purpose and necessity?

Today, everyone involved in corporate operations handles some kind of confidential information, and information security education is becoming increasingly important. This is because even if hardware and software are in place, if each individual lacks security awareness, an external attack or human error could lead to a serious accident.
In this issue, we will explain the necessity, purpose, and implementation method of information security training. We will also introduce contents and materials useful for implementing the training, so please refer to them.
Fundamentals of Information Security Education

To protect companies from information security incidents caused by cyber attacks or mismanagement of information assets, it is important to conduct employee training to strengthen security awareness. First, we will inform you of the necessity, benefits, and purpose of information security education.
Necessity and benefits of information security education
Thorough information security education for employees will make it easier to prevent information leaks. This is because more than 60% of all information leaks are caused by human error, including "lost and misplaced," "mishandling," "mismanagement," "setting," and "theft. It is also expected to reduce risks such as compensation for damages and loss of social credibility due to accidents.
2018 Survey Report on Information Security Incidents|Japan Network Security Association
Purpose and Role of Information Security Education
Ensure that all employees are aware of the information security policy.
Information security policy is a policy for information security measures in a company or organization. It mainly describes action guidelines, plans and measures, as well as operational systems and regulations.
To improve information security awareness within an organization, it is necessary to have ongoing efforts and mechanisms to ensure that all employees comply with the established policies. For example, the penalties for non-compliance and the damage to the organization should be indicated, tests to check the level of understanding should be conducted, and rules regarding the handling of personal information should be thoroughly enforced.
Understand information security threats and countermeasures
In information security training, it is also important to convey real-life examples to ensure that employees comply with the policies that have been developed. For example, it is effective to explain Internet threats and damages, basic measures such as anti-virus and vulnerability countermeasures, and preparedness in handling e-mails and tools.
Back to ContentsHow to systematically promote information security education

The following is a step-by-step explanation of how to implement information security education. Implement information security training in an appropriate cycle and use it to improve your company's literacy.
Step 1: Establish educational objectives and learning themes
Clarifying the objectives at the outset will make it easier to be consistent in your efforts and effectiveness. Extract and organize past incidents and issues related to information security within the company to help set objectives. In addition, from external examples, risks that have not occurred in the past but could occur in the future can be assumed.
Once you have established the objectives of your information security training, determine the security knowledge and skills you want your employees to acquire to solve the problem, and select learning themes that align with these objectives. Examples of learning topics include the following
- Risk of information leakage
- duty of confidentiality
- Types of Confidential Information
- Targeted Attack Email Threats and Countermeasures
- SNS Usage Rules
- Importance of managing information terminals
- Security risks in the use of cloud services and public wireless LANs
- Latest cyber-attack tactics
- Password Management
Step 2: Select the target audience for education
Next, select the target audience based on the purpose of the education and the learning theme. Depending on the content of the training, the target may be determined with reference to the department, position/role, or office location. For example, the target audience may include regular employees of the sales department, outsourced employees involved in business operations, and regular employees of the Tokyo office.
Select all persons involved in the business, regardless of employment status, such as temporary employees, contract employees, part-time workers, and subcontractors, as the target audience.
Step 3: Determine the timing and frequency of education
The next step is to determine the timing and frequency of information security training in order to incorporate it into the schedule. Possible times for implementation include when new or mid-career employees join the company, when a security incident occurs at the company or another company, or when internal rules are changed.
The key is to do this at a time when employee interest in information security is growing.
The frequency of implementation can be once a year, once a month, or once every half year or quarter. The frequency should be determined based on the importance of the content and the frequency of personnel changes, and should be held on a regular basis.
Step 4: Select the form of education and prepare contents
The next process considers the form of information security training to be conducted. Group training, e-learning, and outside seminars are commonly used. Select the appropriate method according to the content of the training, the cost, and the level of literacy of the participants.
A particularly recommended method of implementation is through e-learning. In this form of learning utilizing the Internet, learners access an online server with a computer or tablet and take the required courses.
Because there is no need to gather participants as is the case with group training, and access is possible regardless of location or time as long as there is an Internet environment, it is easy to use even for companies that have introduced remote work.
Once you have decided on the form of education, start preparing the content. Prepare materials that will enable students to acquire the knowledge and skills they seek by creating original teaching materials or purchasing existing content.
In the case of e-learning, depending on the service, it is possible to deliver not only existing content but also a combination of materials produced in-house.
Step 5. follow up based on measurement of effectiveness of education
After the information security training is conducted, measure its effectiveness through confirmation tests and questionnaires. If the results indicate that any employee has a problem with information security awareness, provide feedback and follow-up.
In cases where the company provides its own educational materials, it is also important to review the content based on effectiveness measurements.
Content and materials that can be used for information security education

When conducting information security education, it is efficient to combine external content and materials in a form suitable for your company. Here we introduce content and materials that can be used for information security education.
IPA "Bookmark of Countermeasures"
This is a document made available to the public by the Information-technology Promotion Agency, Japan (IPA), which is under the jurisdiction of the Ministry of Economy, Trade and Industry (METI) IPA conducts activities such as human resource development to strengthen competitiveness in the IT field in Japan.
Specific security measures are introduced according to the purpose and occasion, such as web conferencing, telework, and long vacations, and may be used as training materials or handouts.
Countermeasure Booklet | IPA Information-technology Promotion Agency, Japan
Ministry of Internal Affairs and Communications, "Cyber Security Site for Citizens"
The Ministry of Internal Affairs and Communications (MIC) website provides content on cyber security measures in companies and organizations. The curriculum is divided by roles, such as executives, employees, and information management personnel, making it easy to use for company-wide information security education.
All of the contents are available in downloadable PDF versions, so they can be distributed as handouts after the education has been conducted to help consolidate knowledge. Some of the courses are also available in video format, allowing students to repeatedly watch the expert's explanations.
Cyber Security Site for Citizens | Ministry of Internal Affairs and Communications
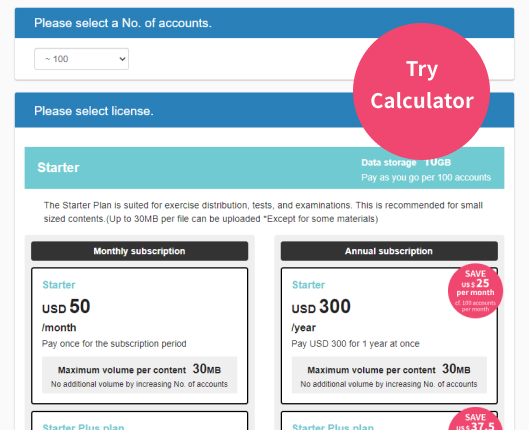
e-learning service learningBOX ON
「learningBOX ONis an e-learning creation and management system, " learningBOXThis service makes it easy to add training content that is essential for companies to "Information Security". The service is also attractive in that you can use the content of our information security materials free of charge and deliver a combination of original teaching materials and existing content.
Back to ContentsLet's promote information security education to make our companies more resilient to cyber risks!
In this issue, we explained the purpose of information security education and how to implement it. To reduce risks such as damage to the corporate image and compensation for damages caused by information security incidents, it is necessary to improve the security awareness of each and every employee. Implement information security education systematically to realize an organization that is resilient to cyber risks.
When informing people about information security in your company, you can use learningBOX ON's
Content is recommended. and other contents are also available free of charge, so please use them for your in-house training.
▼You may also like:
Back to Contents Back to Article List